SA targeted by British and NSA spooks
Foreign politicians and officials who took part in two G20 summit meetings in London in 2009 had their computers monitored and their phone calls intercepted on the instructions of their British government hosts, according to documents seen by the Guardian. Some delegates were tricked into using internet cafes which had been set up by British intelligence agencies to read their email traffic, according to a report in the Guardian newspaper. This follows the defection from the US of National Security Agency whistleblower Ed Snowden in recent weeks. This is the latest in a rash of embarrasing disclosures (for the US and Britain) emanating from the Snowden revelations.
According to the Guardian, the disclosure raises new questions about the boundaries of surveillance by GCHQ (Government Communication headquarters, Britain's spying HQ) and its American sister organisation, the National Security Agency (NSA), whose access to phone records and internet data has been defended as necessary in the fight against terrorism and serious crime. The G20 spying appears to have been organised for the more mundane purpose of securing an advantage in meetings. Named targets include long-standing allies such as South Africa and Turkey.The revelation comes as Britain prepares to host another summit on Monday – for the G8 nations, all of whom attended the 2009 meetings which were the object of the systematic spying. It is likely to lead to some tension among visiting delegates who will want the prime minister to explain whether they were targets in 2009 and whether the exercise is to be repeated this week.
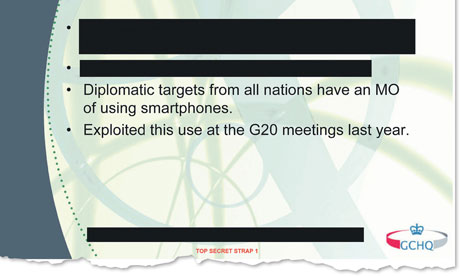
There have often been rumours of this kind of espionage at international conferences, but it is highly unusual for hard evidence to confirm it and spell out the detail. The evidence is contained in documents – classified as top secret – which were uncovered by the NSA whistleblower Edward Snowden and seen by the Guardian. They reveal that during G20 meetings in April and September 2009 GCHQ used what one document calls "ground-breaking intelligence capabilities" to intercept the communications of visiting delegations.
This included:
• Setting up internet cafes where they used an email interception programme and key-logging software to spy on delegates' use of computers;
• Penetrating the security on delegates' BlackBerrys to monitor their email messages and phone calls;
• Supplying 45 analysts with a live round-the-clock summary of who was phoning who at the summit;
• Targeting the Turkish finance minister and possibly 15 others in his party;
• Receiving reports from an NSA attempt to eavesdrop on the Russian leader, Dmitry Medvedev, as his phone calls passed through satellite links to Moscow.
The documents suggest that the operation was sanctioned in principle at a senior level in the government of the then prime minister, Gordon Brown, and that intelligence, including briefings for visiting delegates, was passed to British ministers.
A briefing paper dated 20 January 2009 records advice given by GCHQ officials to their director, Sir Iain Lobban, who was planning to meet the then foreign secretary, David Miliband. The officials summarised Brown's aims for the meeting of G20 heads of state due to begin on 2 April, which was attempting to deal with the economic aftermath of the 2008 banking crisis. The briefing paper added: "The GCHQ intent is to ensure that intelligence relevant to HMG's desired outcomes for its presidency of the G20 reaches customers at the right time and in a form which allows them to make full use of it." Two documents explicitly refer to the intelligence product being passed to "ministers".
 One of the GCHQ documents. Photograph: Guardian
One of the GCHQ documents. Photograph: GuardianAccording to the material seen by the Guardian, GCHQ generated this product by attacking both the computers and the telephones of delegates.
One document refers to a tactic which was "used a lot in recent UK conference, eg G20". The tactic, which is identified by an internal codeword which the Guardian is not revealing, is defined in an internal glossary as "active collection against an email account that acquires mail messages without removing them from the remote server". A PowerPoint slide explains that this means "reading people's email before/as they do".
The same document also refers to GCHQ, MI6 and others setting up internet cafes which "were able to extract key logging info, providing creds for delegates, meaning we have sustained intelligence options against them even after conference has finished". This appears to be a reference to acquiring delegates' online login details.
Another document summarises a sustained campaign to penetrate South African computers, recording that they gained access to the network of their foreign ministry, "investigated phone lines used by High Commission in London" and "retrieved documents including briefings for South African delegates to G20 and G8 meetings". (South Africa is a member of the G20 group and has observer status at G8 meetings.)
Why was South Africa targeted?
Evidently because former President Thabo Mbeki was deemed too independent-minded on the great issues of the day, notably the 2008 economic collapse and what to do about it.
Here's what the Guardian writes:
In December 2005, there was a GCHQ meeting on a project to intensify spying on the South African foreign ministry.
The aim was to "gain access to South African MFA [ministry of foreign affairs] network", to "collect intelligence from target machines" and to "find more access points to increase reliability".
In the corporate-tinged jargon that is pervasive at GCHQ, the desired "customer outcomes" did not involve any suspected nefarious activities by South African diplomats.
This was about spying on their normal work. The objective of the operation was described as acquiring "retrieved documents, including briefings for South African delegates to G20 and G8 meetings".
It is clear that GCHQ was aiming to find out everything it could about the negotiating position of the government of President Thabo Mbeki, an independently minded swing vote on issues of global economics and finance.
Such intelligence collection was carried out under the title "transnational strategic issues" which embraced energy, economics and the environment.
It was a multipronged offensive against the South African foreign ministry under Nkosazana Dlamini-Zuma. The phone lines used by the country's high commission in London were "investigated".
The "computer networks exploitation" (CNE) team, responsible for hacking into foreign computer networks, had acquired passwords from a standing operation whose task it was to wheedle them out of target governments and agencies.
One line of approach was to dig up the old phone numbers and email addresses of the head of the cryptology department in Pretoria. The passwords were then used to hack into the online accounts of South African diplomats.
The task was complicated by the fact that the South African foreign ministry had recently upgraded its networks, but the new passwords to the system appear to have been rapidly acquired, and the CNE team set up a series of back doors into the ministry networks "to increase reliability" of the hacking operation.
















